OWASP Top 10 Pentesting
OWASP Top 10 Pentesting & Compliance
Get quality, comprehensive pentesting, carried out by expert ethical hackers. Cyver delivers OWASP Top 10 Pentests in our Pentest-as-a-Service Platform, so you stay secure.
OWASP Top 10 Assessment
Resolve major security issues and meet compliance needs with our standard OWASP Top 10 Penetration Test. Cyver delivers fast, insightful testing on every major vulnerability, so your organization can identify and remediate vulnerabilities. We deliver pentests in our pentest management platform, with vulnerabilities mapped by criticality, and the report mapped to the OWASP Top 10 so you can see how and where your organization is at risk.
Do I Need an OWASP 10 Assessment?
For many organizations, OWASP Top 10 represents the bare minimum standards to which you must be secure. Small websites and applications, which do not process sensitive data themselves can utilize the OWASP Top 10 for routine compliance and security. Larger organizations, and those that process sensitive data, should utilize OWASP Top 10 as a standard checkpoint during development and before big releases. If you need a pentest for compliance needs, you may want an ASVS Level 1, Level 2, or Level 3 assessment instead.
An OWASP Top 10 pentest checks your web properties for routine issues. This guideline is defined by the Open Web Application Security Project, to help organizations set standards for security and to change how web applications are built and secured. Our pentest can help you ensure you meet those standards.

What’s Included in an OWASP 10 Pentest?
Cyver delivers comprehensive OWASP Top 10 pentesting, in line with OWASP guidelines. This includes blackbox checks for the 2021 Top 10 vulnerabilities, with methods and standards updated according to organization-specific requirements.
- Broken Access Control
- Cryptographic Failures
- Injection
- Insecure Design
- Security Misconfiguration
- Vulnerable and Outdated Components
- Identification and Authentication Failures
- Software and Data Integrity Failures
- Security Logging and Monitoring Failures
- Server-Side Request Forgery
Cyver will onboard you to our cloud platform, where we will set scope, help you define assets, and begin testing
Report
Request a Free OWASP Top 10 Sample Report
Request a free sample report to see how Cyver delivers pentest reports OWASP Top 10. We’ll onboard you to our platform, where you can see and interact with sample findings as tickets, compliance data, and the full pentest report.

Pentest-as-a-Service
We make OWASP Top 10 compliance digital, with a cloud platform, automated alerts, and real-time collaboration. Our OWASP Top 10 solution is centered around collaborative pentesting and resolving findings. That’s why we onboard your developers to our platform, issue real-time alerts as findings are updated, and offer one-on-one communication with pentesters. Plus, with pentest-as-a-service, your next pentest is scheduled as part of the existing one, so you stay secure, long-term.
Secure Development
Integrate security directly into your development cycles, with scheduled pentesting that works with your teams. Our simple credit system means developers can utilize pentest budgets to request OWASP Top10 assessments as part of development cycles, ensuring security before a release.
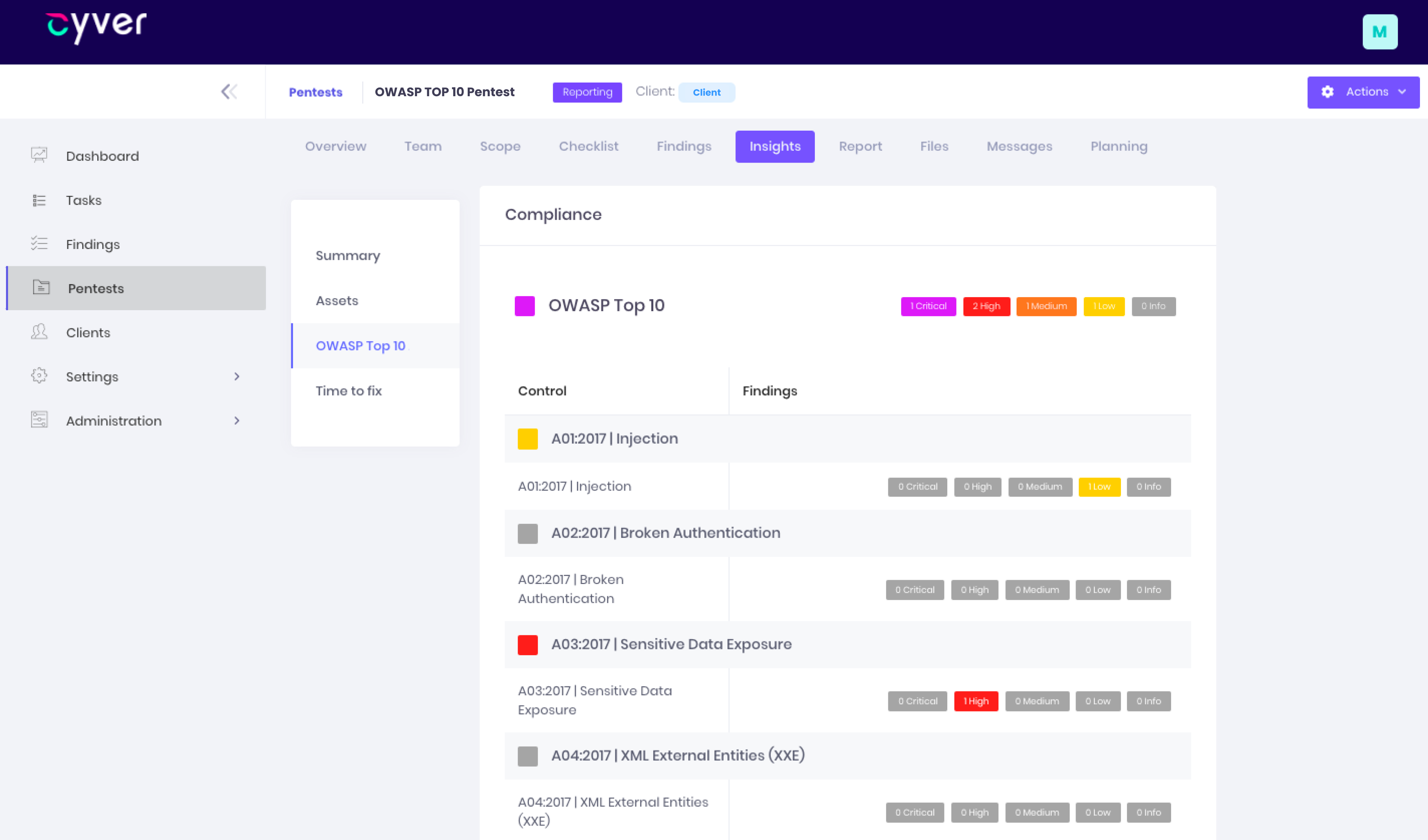
Collaborative Reporting
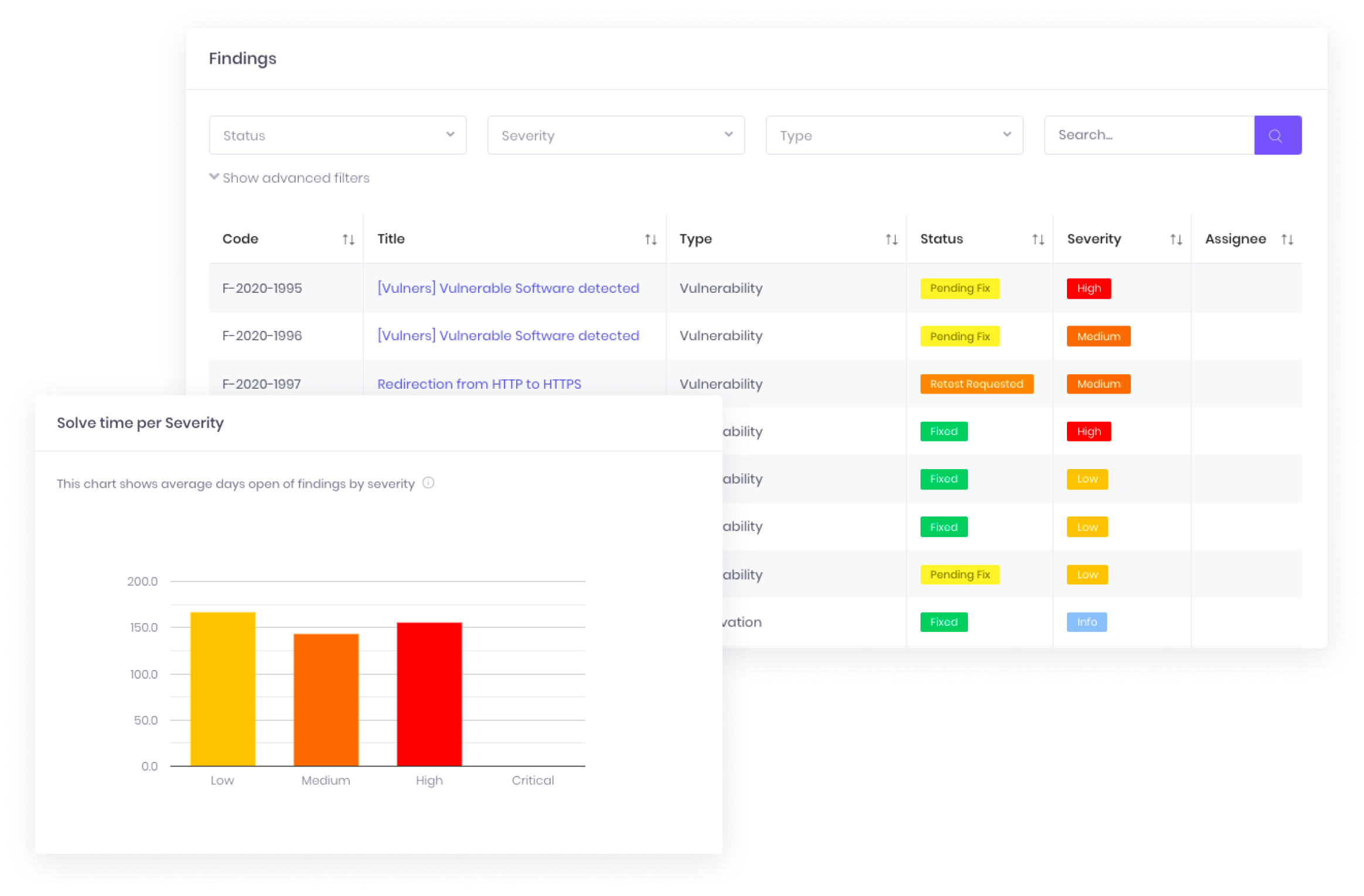
We deliver ticket-based findings through our cloud platform, so stakeholders always stay informed. Cyver helps you resolve issues, with communication, collaboration, and free retests. And, when you need a compliance report, you can automatically generate it based on real-time finding status.
Last-Minute Service
Request a last-minute pentest, or schedule up to a year in advance. Cyver leverages OWASP Top 10 Frameworks and cloud project management, with ticket-based reports, so projects move as quickly as possible. Lead times for OWASP Top 10 pentests can be as little as 5 business days.
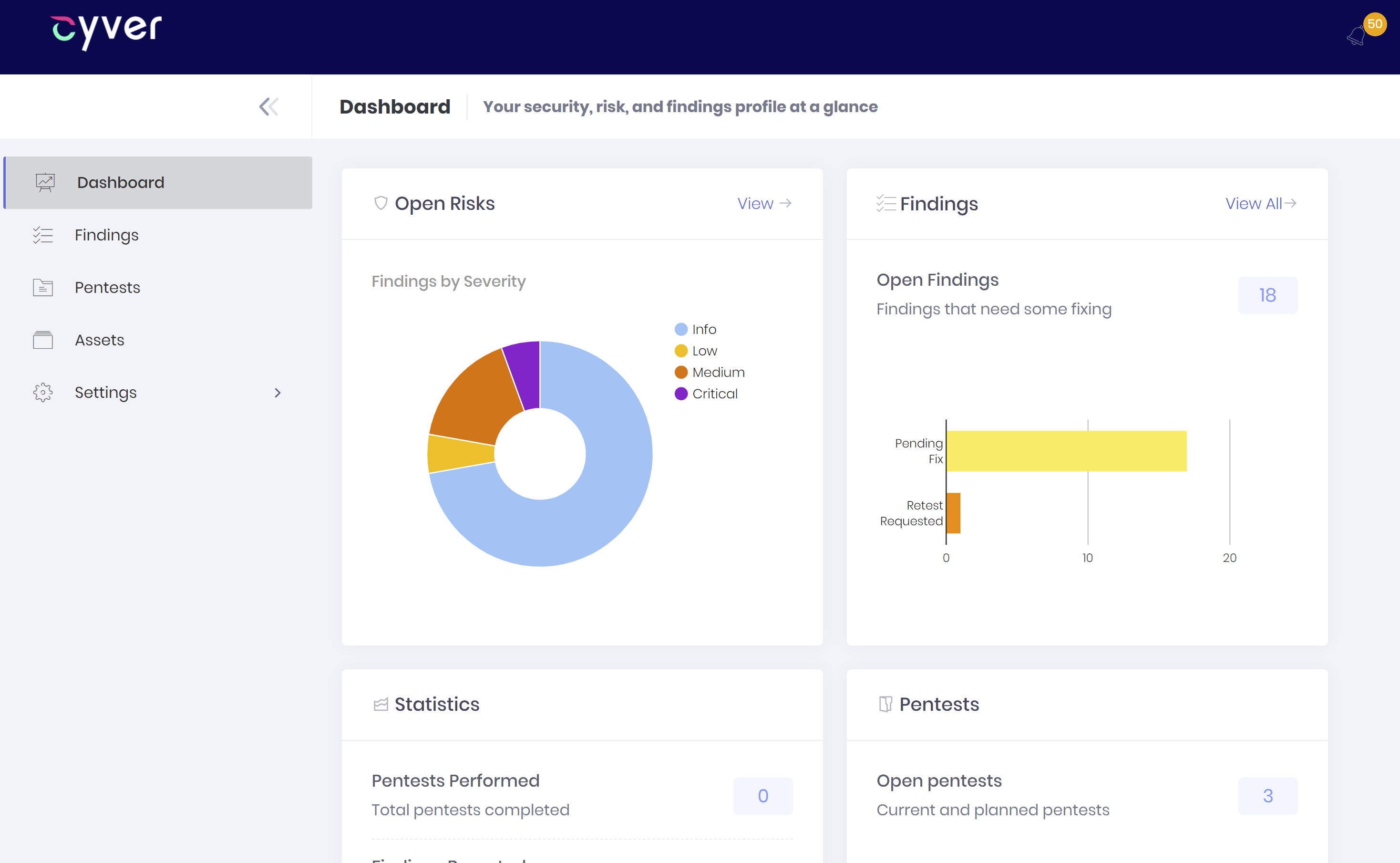
Your Pentest Platform
From onboarding to scheduling ongoing pentests, Cyver is here to make your pentest processes better. We deliver full access to a cloud Security Dashboard, where you can request assessments, see findings in real-time, track findings and proof-of-concept files in one secure place, and automatically assign findings to developers. Our cloud platform delivers findings as tickets, risk analysis, reports, and security metrics. We make pentest reports modern, digital, and actionable.
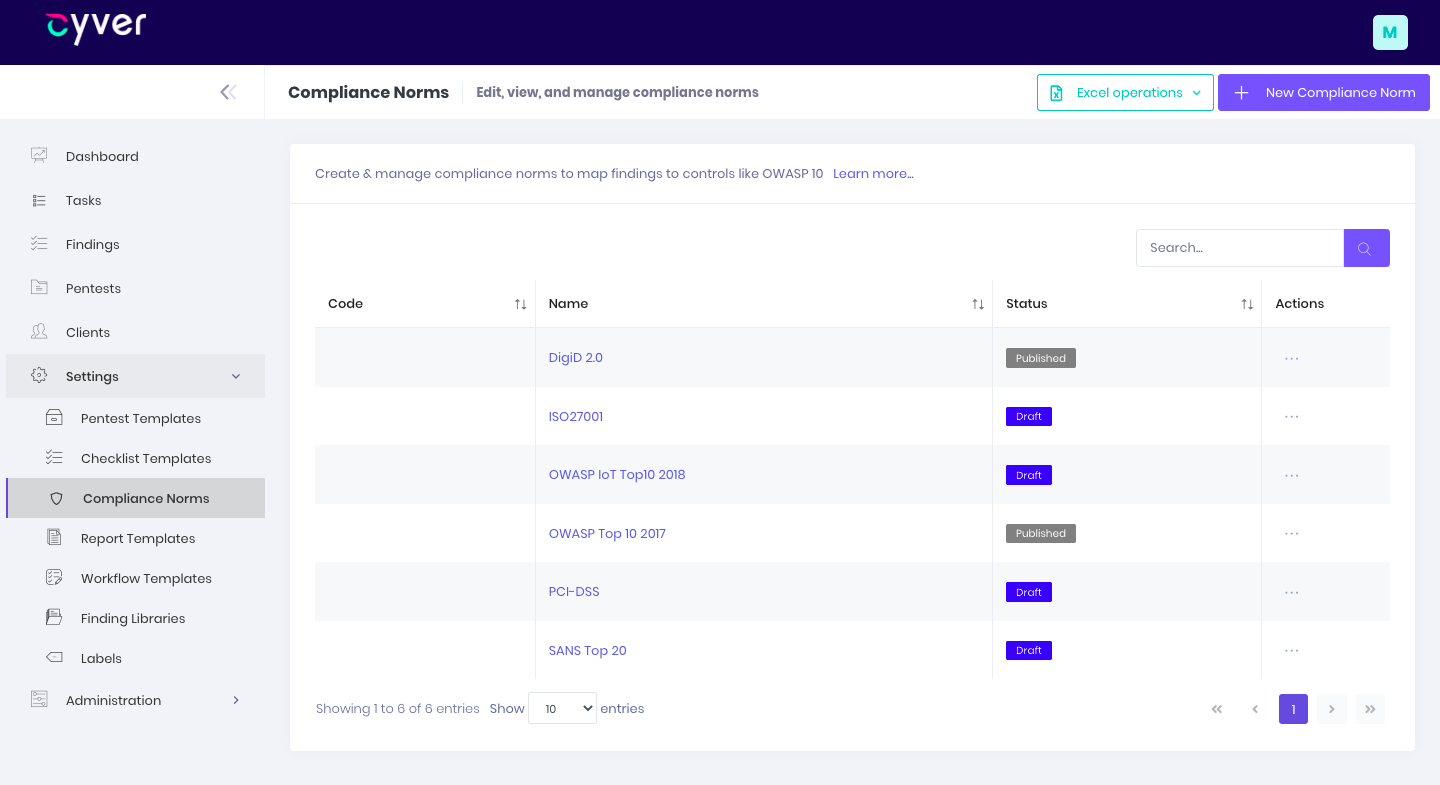
Compliance Frameworks
Other Compliance Norms?
Leverage pentest norms and frameworks to quickly launch assessments with complete oversight of what we’re testing and why. We build norms for PCI, HIPAA, ISO27001, ISAE3402, and more based on official recommendations. Plus, every framework is customizable to client needs and specifications.
Any questions?
We are here to help
What is a Pentest-as-a-Service
Pentest-as-a-Service combines our human expertise and insight with the convenience of cloud apps and findings-as-tickets. We organize pentests in our cloud platform, Cyver Core, and deliver pentest reports with tickets, so developers and compliance officers can remediate right away. Plus, we offer free insight tooling, so you can see remediation times, risk profiles, and even areas of risk.
When Can You Start?
In most cases, we can start your pentest within 2 weeks. In some cases, we can finalize and deliver your pentest during that time. However, pentest duration depends on the scope of the pentest, your assets, and environments.
Cyver leverages a network of pentesters, allowing us to quicly scale to meet demand. When you need expert pentesters, we can help, and quickly. If you want a quote based on your specific needs and assets, book a demo now for a one-on-one conversation.
How Much Do You Charge for a Pentest?
Cyver uses a credit system to charge a flat rate for our pentests. That means costs are always transparent and you always know what you're paying for. Currently, we charge €329 per pentest credit. Pentests range from 2 credits for a simple 1-website test to well over 40 credits for a large and complex system. Visit our pricing page for more information.
What Does the Platform Look Like?
Visit our How it Works page to see Cyver in action. Or, schedule a demo to see it live. Our platform, Cyver Core, allows you to onboard your full team, assign responsibilities, and see findings results in real time. When we deliver the report, you can export it to a PDF or process it as tickets, linked to tooling like Jira, for faster remediation.