Our Report Methodology
Cyver’s Pentest Report
Cyver invests in high quality reporting to ensure you get the information you need from every pentest. That, plus our digital delivery via the pentest platform, means you’ll have clear oversight of vulnerabilities, risks, and compliance needs.
We work with diverse pentest and cybersecurity partners. Therefore, your final report will depend on your partner. However, we strive to deliver our pentest reports within the following guidelines.

Management Summary
We offer clear oversight of the pentest and vulnerability findings in non-technical language. This section of the report is ideal for management and non-technical stakeholders who need an overview of information.

Pentest Overview
The management summary offers a brief overview of the full pentest, to keep management and stakeholders in-the-know.
Risk Management
See which assets are impacted, relevant criticality, and how vulnerability findings impact risk as a whole.

Finance and Budgeting
Share management summaries with stakeholders responsible for budgeting for future pentests and for remediation.
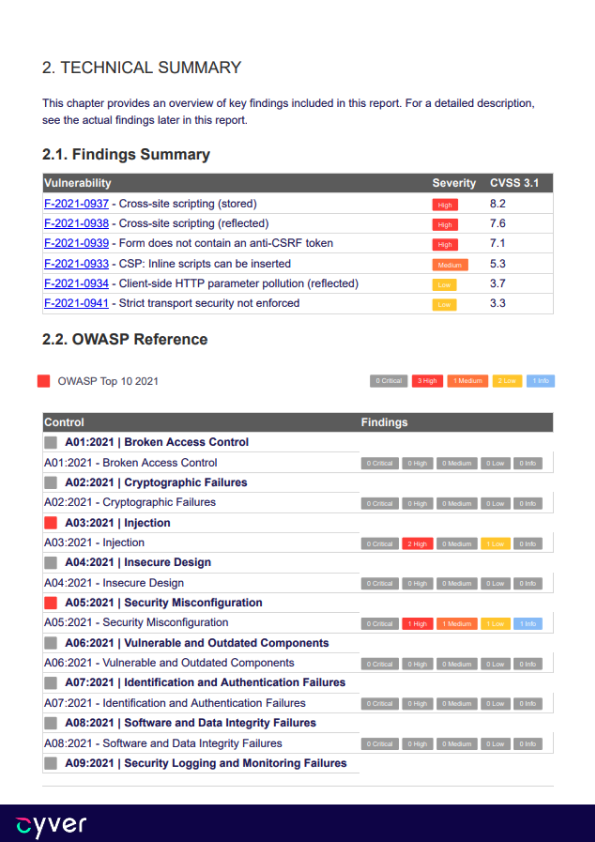
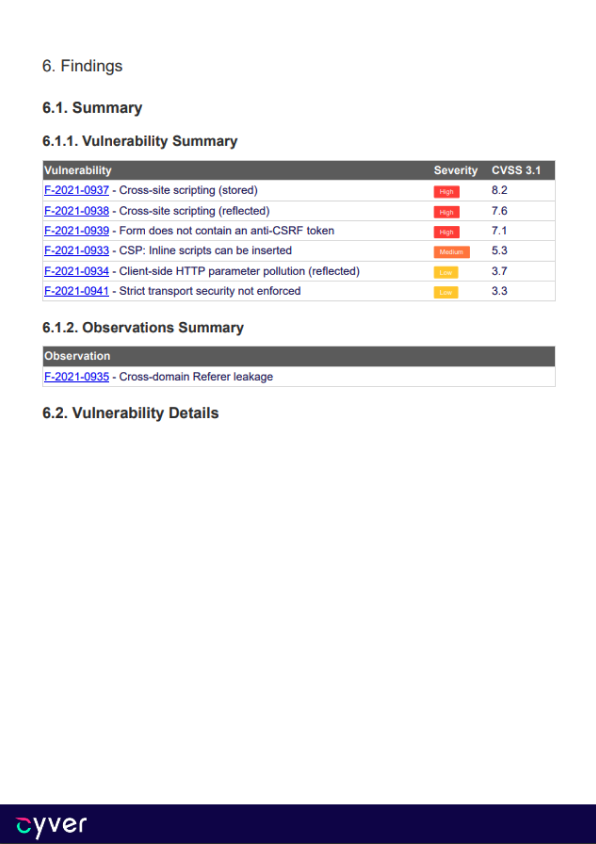
Technical Summary
A full list of findings including risk mapping, for technical readers.
Report Card
Get a full overview of found vulnerabilities, mapped by criticality, and to assets, for a full risk report card for your organization.
CVSS Scoring
We use CVSS scoring to ensure you always have a way to assess criticality and to prioritize fixes – so devs know where to start.
Findings
This section includes a full list of findings without added technical details, for easier reference and management.
Assignment
Cyver delivers a full list of scope, pentest details, checklists used, etc. as part of the pentest report.
Pentest Scope
This includes assets checked, the attention payed to each asset, and full details about what was checked and why.

Pentesters
We ensure you know who is pentesting your application and that you can contact them after the fact for help with remediation.
Checklists
Cyver delivers a full checklist of tasks performed during the pentest, so you can see what was checked and why for better oversight.
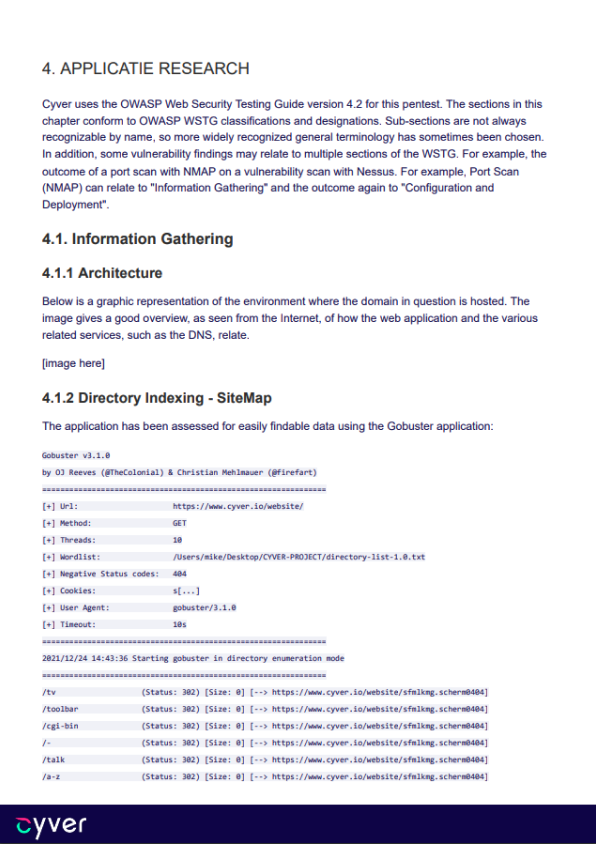
Methodology
Get insight into tooling, source, and approach for the pentest – for transparency, and to enable finding replication.
Compliance
Meet compliance needs with compliance requirements built into the report. If you’re testing for audit purposes, we add a relevant section to your report to help you pass the audit.

Frameworks Used
See relevant compliance frameworks used during the pentest so you can easily decide what to show the auditor.

Vulnerability Mapping
Cyver maps vulnerabilities to your compliance framework, so the report automatically shows how findings fit into compliance.
Checklists
Show compliance with a full checklist of tasks and assessments performed during the pentest for better transparency during the audit.
Findings
Get a full list of vulnerability findings, complete with tickets, replication data, remediation advice, and general information.
Finding Data
Cyver shares all of the information we have on a vulnerability finding including CVSS scores, general information, and CVE listing.
Remediation Tips
If we have suggestions to remediate a vulnerability, we provide it as part of the report, linked to the relevant finding.

Replication Data
We share methodology and tools used to find the vulnerability, so your devs can more easily find, recreate, and resolve it.
Proof of Findings
We use screenshots, source, and attack paths to show proof of findigns whenever possible to simplify your path to remediation.
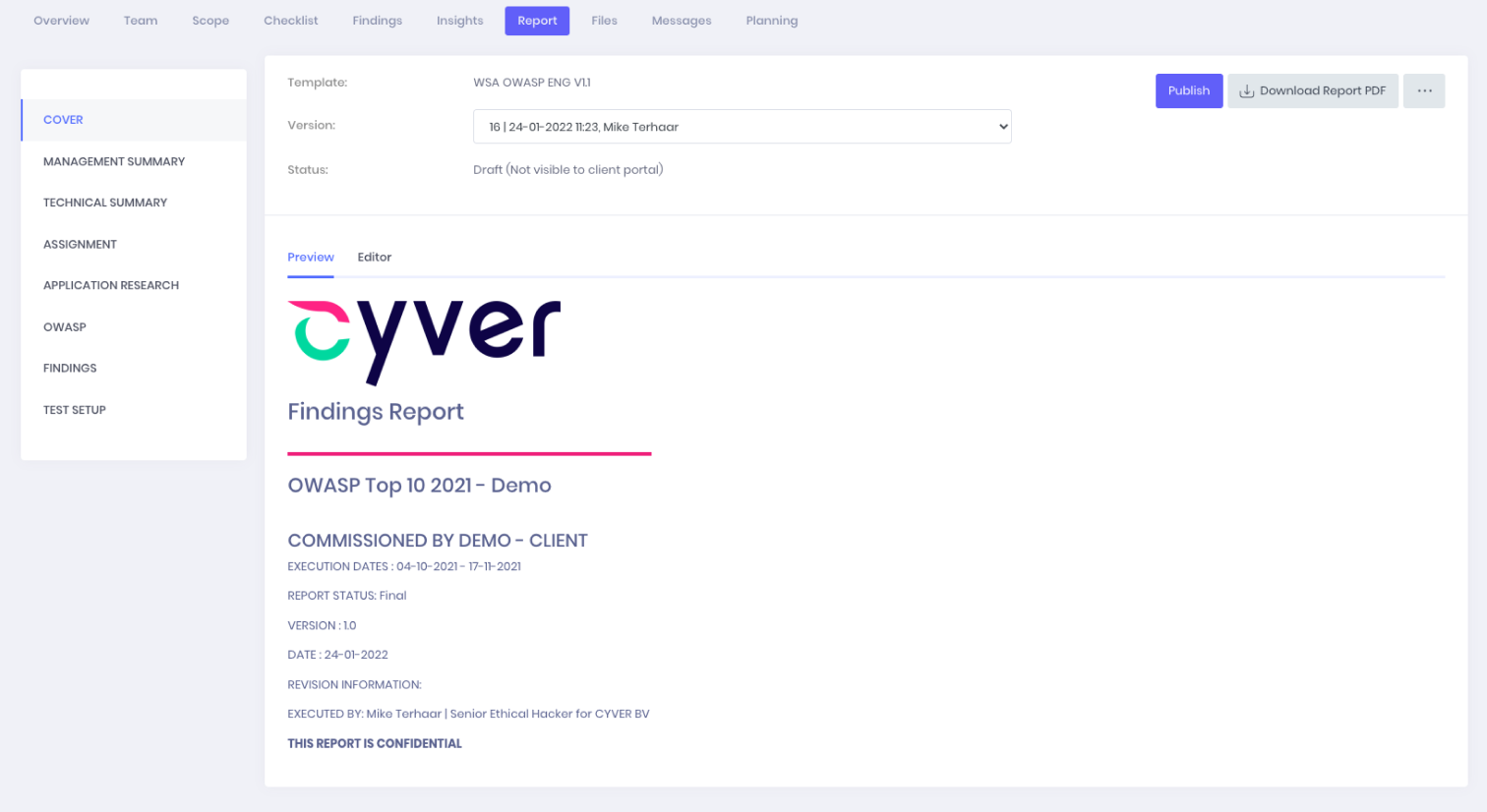
Pentest Platform
When you onboard with Cyver, you get more than a PDF report. We’re proud of our reports. But, we also deliver interactive data, including live findings ast tickets, via our pentest-as-a-service platform.

Findings-as-Tickets
We upload findings as tickets, linked to assets, rated for criticality – so you can export to Jira, and immediately work on remediation.
Live Notifications
Onboard your team, set responsibilities, and we’ll automatically alert stakeholders when their asets have a vulnerability.
Security Dashboard
See open vulnerabilities at a glance, with metrics showing vulnerabilities by criticality, by asset, and by how long each ohave been open.
Report
Request a Free Sample Report
Request a free sample report to see how Cyver delivers pentest reports. We can also onboard you to our platform, where you can see and interact with sample findings as tickets, compliance data, and the full pentest report.
Need a pentest? Contact us for a consultation
Cyver’s team of pentesters are experts in cyber security, ranging from simple websites to complex infrastructure or applets. Contact us to learn more about how we can help secure your application.
Any questions?
We are here to help
What is a Pentest-as-a-Service
Pentest-as-a-Service combines our human expertise and insight with the convenience of cloud apps and findings-as-tickets. We organize pentests in our cloud platform, Cyver Core, and deliver pentest reports with tickets, so developers and compliance officers can remediate right away. Plus, we offer free insight tooling, so you can see remediation times, risk profiles, and even areas of risk.
When Can You Start?
In most cases, we can start your pentest within 2 weeks. In some cases, we can finalize and deliver your pentest during that time. However, pentest duration depends on the scope of the pentest, your assets, and environments.
Cyver leverages a network of pentesters, allowing us to quicly scale to meet demand. When you need expert pentesters, we can help, and quickly. If you want a quote based on your specific needs and assets, book a demo now for a one-on-one conversation.
How Much Do You Charge for a Pentest?
Cyver uses a credit system to charge a flat rate for our pentests. That means costs are always transparent and you always know what you're paying for. Currently, we charge €329 per pentest credit. Pentests range from 2 credits for a simple 1-website test to well over 40 credits for a large and complex system. Visit our pricing page for more information.
What Does the Platform Look Like?
Visit our How it Works page to see Cyver in action. Or, schedule a demo to see it live. Our platform, Cyver Core, allows you to onboard your full team, assign responsibilities, and see findings results in real time. When we deliver the report, you can export it to a PDF or process it as tickets, linked to tooling like Jira, for faster remediation.