HEALTH CARE
Healthcare Pentesing & Compliance
Prepare for audits with pentesting for healthcare standards like ISO 27001, HIPAA, NEN 7510, GDPR, DigiD, and more.
Healthcare Compliance
Healthcare providers and software engineers are bound by dozens of compliance standards intended to protect patient data and privacy. You need pentesting to ensure information security and information systems compliance with standards like HIPAA, GDPR, and ISO 27001. Cyver has partners specializing in pentesting for healthcare and medical compliance, and we will help you find and resolve vulnerabilities before the audit.

Who Needs Healthcare Assessments and Pentests?
While many countries maintain individual healthcare compliance regulations and standards, most of these standards are intended to be as broad as possible. In most countries, any healthcare organization must comply with standards like HIPAA, ISO 27001, or NEN 7510. In addition, most companies developing software and information systems for healthcare companies and patient data must ensure their products comply with local regulation. Healthcare organizations should also consider pentesting for security purposes. IMB shows that breaches cost healthcare organizations 65% more than any other industry, with risks including lost patient and private data, fines, and lost revenue. Pentests help your business secure its web applications and properties, for your organization and your clients.
Which healthcare regulations do you need? That depends on your region(s). The United States uses HIPAA, the Netherlands uses NEN 7510, and ISO 27001 / 2 offers an international standard. Each are similar, but if you operate in three countries, you might have to comply with all three. Check your local regulation for more information.
What’s Included in a Healthcare Pentest?
Cyver delivers healthcare pentests according to a range of different norms under different standards. These typically include a pentest of information security systems using grey-box testing.
Most healthcare pentests are performed to OWASP Testing standards, incorporating significant security verification to demonstrate good security, architecture, and coding design. Pentests must be performed with access to the system (grey-box/white-box), and include checks for controls and processes for confidentiality, integrity, authentication, non-repudiation, and authorization of data. Other standards change depending on the specific audit or pentest in question. Contact us for more information.
Pentest-as-a-Service
Cyver makes healthcare compliance simple, with a cloud platform designed to offer real-time alerts and collaboration. Our pentests aren’t delivered as 60-page reports, you get live tickets, real-time communication with hackers, and updates, so you can resolve vulnerabilities and generate a clean report in time for your audit.
Comprehensive Testing
Cyver will help you set the scope to define assets while onboarding you to our cloud platform. We completely customize each pentest to meet your compliance needs, with a full assessment of impacted infrastructure, components, and applications, so every aspect of your platform is secure and compliant.
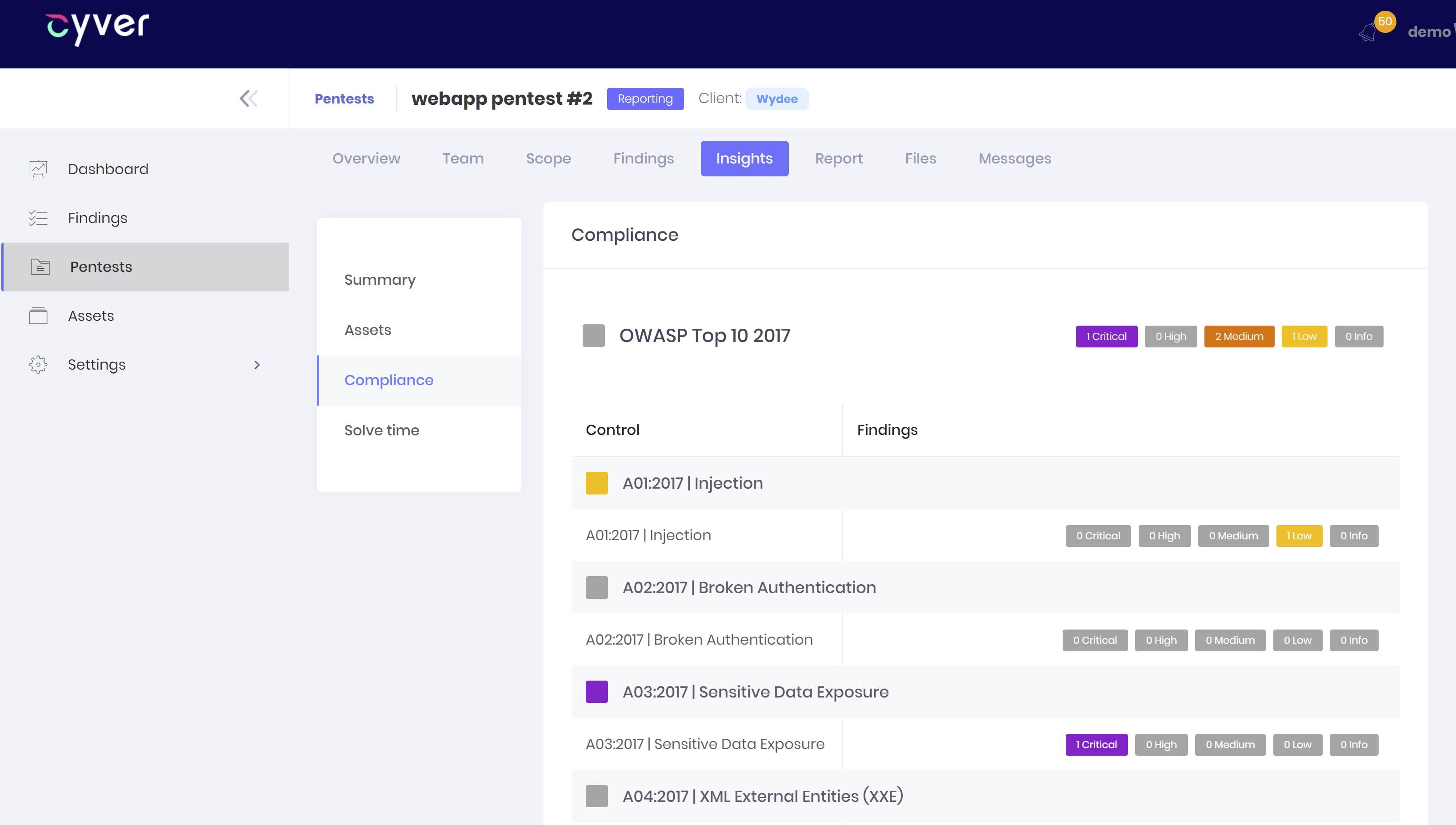
Digital Reporting
Our digital reporting and ticket system means reports are always up-to-date. Plus, with automatic reporting, you can generate your report at any time, using live data. Collaborate with our developers to resolve findings and then generate a clean pentest report to ensure your audit goes as smoothly as possible.
Fast Service
Unprepared for your audit? If compliance reports are due, Cyver is here to help. Our digital platform cuts lead times using automation, real-time communication, and a flex workforce. Whether you need ISO 27001 / 2, HIPAA, NEN 7510, or others, we’’ll prioritize your pentest at no added cost.
Other compliance norms?
Leverage pentest norms and frameworks to quickly launch assessments with complete oversight of what we’re testing and why. We build norms for PCI, HIPAA, ISO27001, ISAE3402, and more based on official recommendations. Plus, every framework is customizable to client needs and specifications.
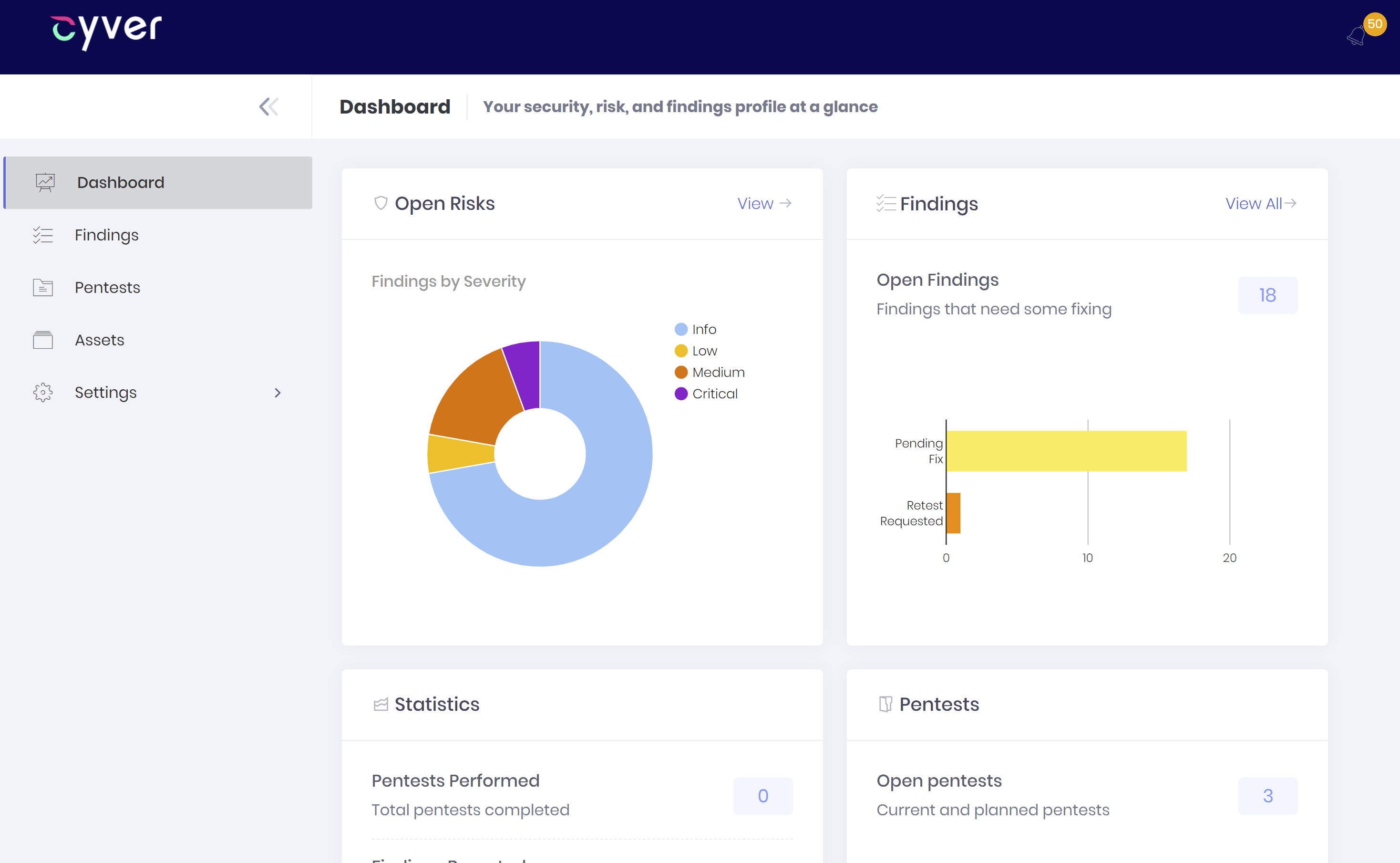
Your Pentest Platform
From onboarding to scheduling ongoing pentests, Cyver is here to make your pentest processes better. We deliver full access to a cloud Security Dashboard, where you can request assessments, see findings in real-time, track findings and proof-of-concept files in one secure place, and automatically assign findings to developers. Our cloud platform is designed around helping you with findings, risk analysis, reports, and your security environment, with communication, collaboration, and actionable reports.