Network & Infrastructure Pentesting
Pentest Networks & Infrastructure
Secure networks to meet compliance needs, prevent intrusion, and identify vulnerabilities, with a NIST or PTES compliant network pentest from Cyver.


Pentesting Your Network
We assess open ports, access controls, and devices to find and exploit entryways into networks, exploit those vulnerabilities, and assess the full security of your infrastructure. Cyver pentests infrastructure in a live environment, according to rules of engagement – based on your infrastructure requirements. Plus, with full compliance to and PTES and NIST 800 standards, we offer the best possible assessment of your network security.

Public Cloud
Assess infrastructure, configurations, and access controls across the public cloud. Cyver is experienced in pentesting AWS, Azure, Google Cloud, and more.

Networks
Assess for access points, open ports, outdated systems, software issues, and other vulnerabilities, with a manual review and human insight to identify weaknesses.

On-Premise
Dutch and Benelux clients can request local assessments of on-premise servers, databases, and networks, with assessments performed to a platform level.

Client Workstations
Cyver performs a pentest on the full network by attempting to hack into client workstations, access data and servers, and exploit available weaknesses.
Expert, Ethical Hacking
We perform pentests to PTES and NIST 800 standards, map vulnerability findings to compliance norms, & deliver in our cloud platform.


Expert Pentesters
Cyver’s network of expert ethical hackers allows us to choose the best pentester for your network, cloud, and servers.
Manual Testing
We take a “best of both worlds” approach, aligning manual testing with scanning, for up to 80% manual review of your network.

Pentest Standards
We pentest based on guidelines from NIST 800 and PTES, with checklists to ensure compliance and alignment with quality standards.
Rules of Engagement
Cyver pentests live networks, following rules of engagement set by you or your suppliers, to ensure networks and data stay safe.
Pentests Delivered in the Cloud
Cyver delivers scheduled, recurring pentests across updates, compliance periods, and feature rollouts to keep your networks secure.

Recurring Pentests
Schedule pentests on a monthly, quarterly, or yearly basis – or plan pentests according to Agile team development.

Asset Management
Upload and share assets like IPs, domains, and databases to link specific assets to vulnerability findings.

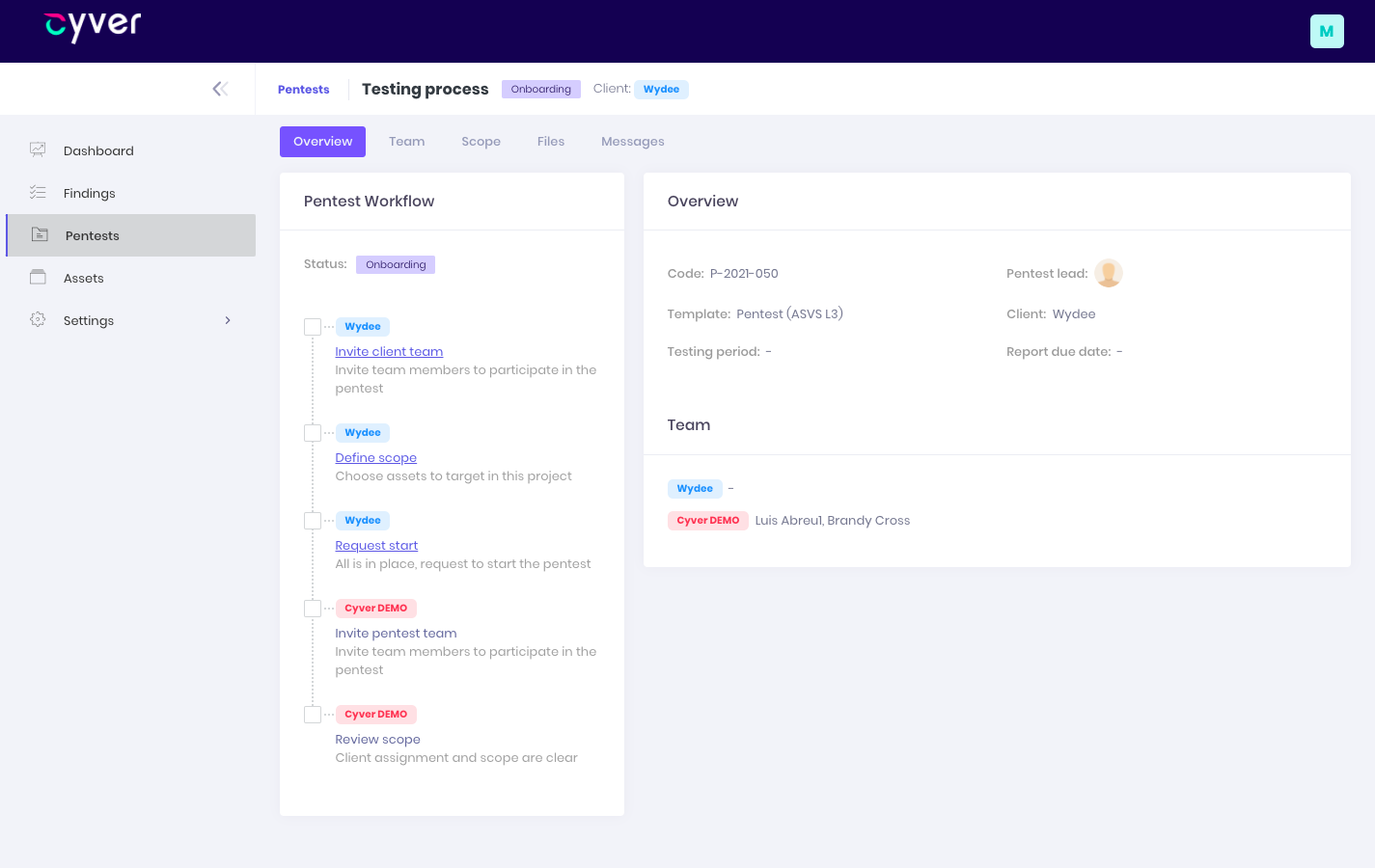
Onboard Your Team
Onboard to our platform to see real-time alerts, so dev teams can immediately work on vulnerability remediation.
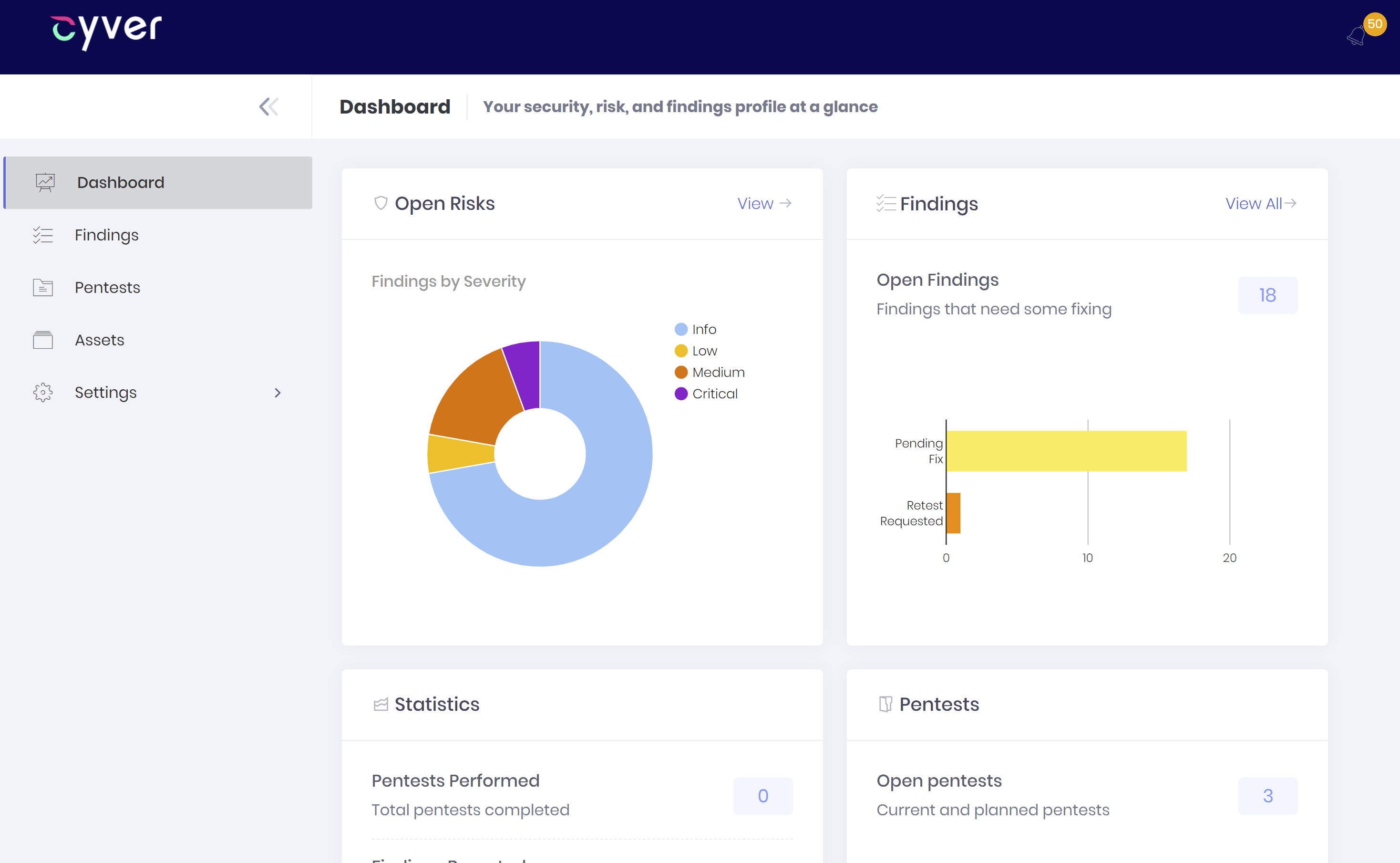
Vulnerability Metrics
Get more than a report with vulnerability metrics across assets, vulnerability profile, and CVSS scores for long-term management.
Agile-Friendly Pentest Delivery
Put IT and compliance officers in control of security with the timely information and communication they need to remediate vulnerabilities.
Findings-as-Tickets
Get findings as tickets and manage them in Cyver’s platform or link to platforms like Jira to assign tickets in your existing tooling.
Assigned Tickets
Assign teams to vulnerabilities, export tickets to tooling, and track remediation so you always know what was fixed and when.
Pentest Credits
Budget for pentests upfront, buy credits, and use them towards flat-rate pentests – so devs can align pentests with updates.
Request a Pentest
Skip lengthy RFP processes and request a pentest, in the platform – using specs and assets from your last, for simple re-testing.
Meet Compliance Obligations with Cyver
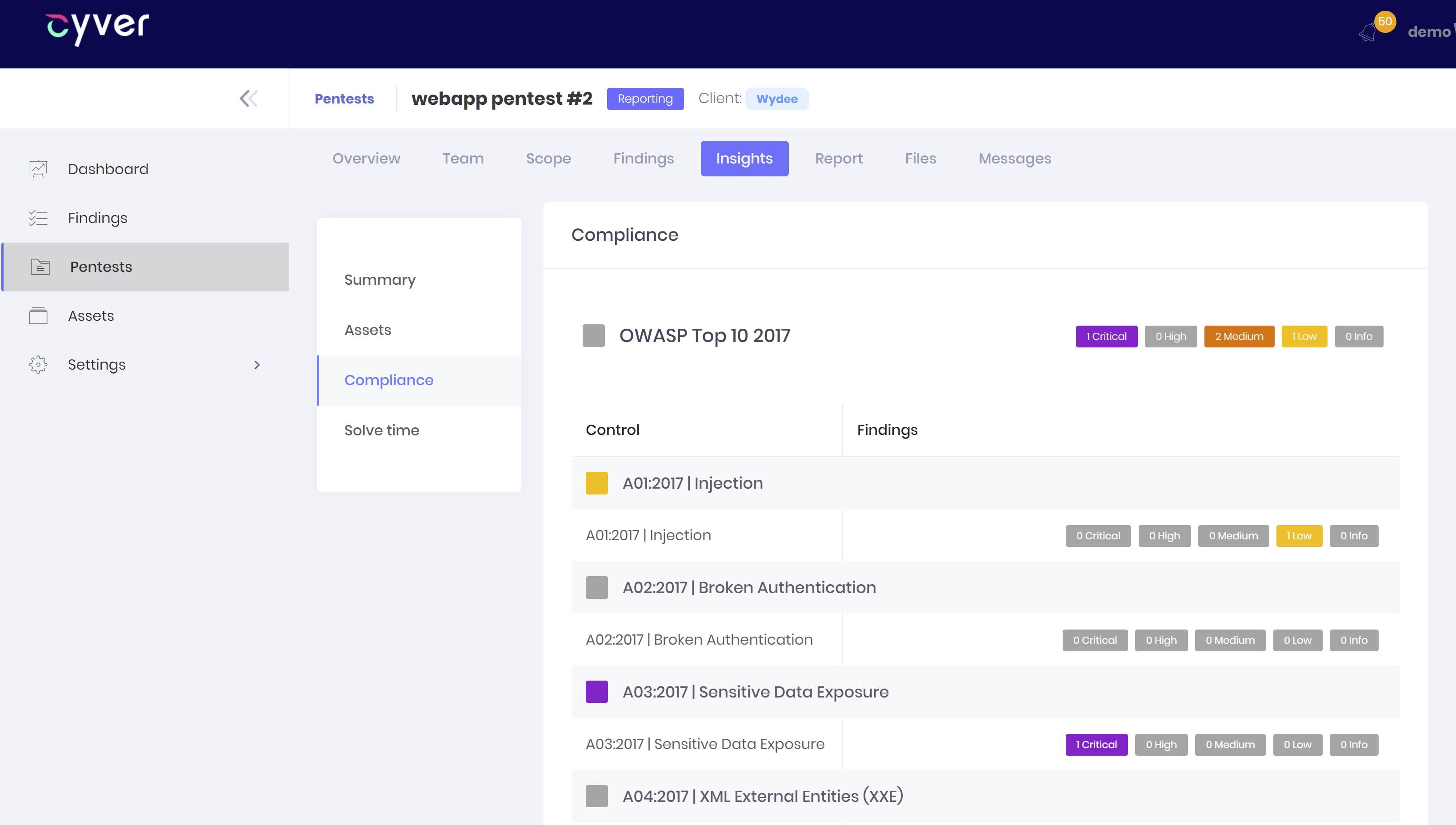
Cyver helps you achieve compliance with pentesting mapped to compliance norms like NIST 800 + PTES standards, for compliance with PCI-DSS, etc.
Compliance Frameworks
Cyver pentests using compliance frameworks and checklists to ensure we fully meet your compliance needs.
Findings as Tickets
Collaborate on remediation with real-time chat and free retesting for 30 days after the initial pentest, to ensure fixes work.

Compliance Reports
We deliver reports with vulnerability findings mapped to compliance norms, and audit sections, to simplify audits.
PDF Downloads
Generate a PDF report of the current vulnerability status after retesting fixed findings, so your auditor receives a clean report.
Need a pentest? Contact us for a consultation
Cyver’s team of pentesters are experts in network and infrastructure security, ranging from the public cloud to on-premise servers. Contact us to learn more about how we can help secure your organization.
Any questions?
We are here to help
What is a Pentest-as-a-Service
Pentest-as-a-Service combines our human expertise and insight with the convenience of cloud apps and findings-as-tickets. We organize pentests in our cloud platform, Cyver Core, and deliver pentest reports with tickets, so developers and compliance officers can remediate right away. Plus, we offer free insight tooling, so you can see remediation times, risk profiles, and even areas of risk.
When Can You Start?
In most cases, we can start your pentest within 2 weeks. In some cases, we can finalize and deliver your pentest during that time. However, pentest duration depends on the scope of the pentest, your assets, and environments.
Cyver leverages a network of pentesters, allowing us to quicly scale to meet demand. When you need expert pentesters, we can help, and quickly. If you want a quote based on your specific needs and assets, book a demo now for a one-on-one conversation.
How Much Do You Charge for a Pentest?
Cyver uses a credit system to charge a flat rate for our pentests. That means costs are always transparent and you always know what you're paying for. Currently, we charge €329 per pentest credit. Pentests range from 2 credits for a simple 1-website test to well over 40 credits for a large and complex system. Visit our pricing page for more information.
What Does the Platform Look Like?
Visit our How it Works page to see Cyver in action. Or, schedule a demo to see it live. Our platform, Cyver Core, allows you to onboard your full team, assign responsibilities, and see findings results in real time. When we deliver the report, you can export it to a PDF or process it as tickets, linked to tooling like Jira, for faster remediation.